PC Plus HelpDesk - issue 240
This month, Paul Grosse gives you more insight into
some of the topics dealt with in HelpDesk
|
 |
HelpDesk
CD installation-set recognition problem on UNIX-like systems
|
Hidden files in UNIX-like OSes
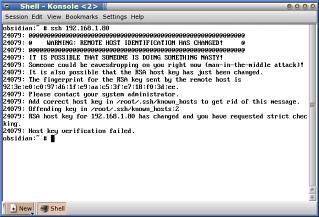
To see these files, you need to be explicit so, in ls, just use 'ls -a'. In Windows, the hidden attribute does the same and, if you are unfortunate enough to have been hit with the Sony Rootkit Trojan, other files will be hidden as well. In Mac OS X (which is very loosely based on FreeBSD although it is more like Windows than BSD), there are two other ways of hiding files:
In Konqueror - as you can see in the screen shot - change the listing view with 'View'/ 'Show Hidden Files'. You can see the same directory but one has the hidden files listed. So, why hide files? Most of the time, it isn't to try to pull the wool over your eyes, it is simply to get them out of the way in normal work. You don't want to see all of your settings directories listed if you just want a normal listing of your home directory. If you do want to see them, doing so is easy, just as it is in DOS. |
Alternative uses for MP3 players
You can either rip your own resources such as CDs for language learning or there are a number of mp3 resources online. Here are a few:
|
TCP FIN scan attacks
Some online chat servers send TCP FIN packets after the connection has closed and these can look to a firewall like an attack. With a hardware firewall (and some software firewalls), you can get it to send you an email whenever this happens. So, when someone says that they have finished half an hour before the firewall has send you a message saying that they did, you can question that legitimately. It is worth pointing out that these apparent attacks (they aren't really attacks but the firewall treats them as possible attacks so that you know if you are really under attack) don't necessarily represent the exact moment that a connection has been dropped. So, if your daughter claims that she finished on here instant messenger at 10:30pm when she was supposed to and you get an email like the one in the screenshot, you know that you can say; 'Computer says; "No".' |
Configuring an SMB printer in SUSE 10.0If you have a printer already established on another machine and that machine tends to be in use all of the time, you can configure your Linux machine to use the printer network share. Note that for security's sake, you have your LAN behind a firewall otherwise, other people will be able to hack your Windows machines
|
WebminIf you have a number of machines on your LAN that you want to configure all remotely, you can do so using Webmin.
Yes, Windows. |
BOGOMIPS
To get to the BOGOMIPS value on a Linux box, just type cat /proc/cpuinfo Note that in order to do this, you need a /proc directory so doing this on OpenBSD will not work as that does not have a /proc directory - there are programs for the BSD OSes though - see the link below. If you are interested in this and run a Windows machine, you can either run KNOPPIX and do as above or, you can download the bogomips Windows executable which can be found at http://hpm101.gotadsl.co.uk/projects/bogobinaries/. Fave fun. |
Open Source Software for Windows
|
PostScipt Sudoku answers from issue 239If you have installed (if you needed to) a Post Script reader of some sort and you have printed out and solved the Sudoku problems I left you with last month, you might like to know the answers to any that you had a problem with. Click here to open up the directory in a new window so that you can see the solution files. |

 If
you run a UNIX-like operating system such as
Linux or one of the BSDs, you could, once you
have everything installed the way you want it,
leave it running without rebooting it for months.
It is also likely that you won't install anything
for a long time as well.
If
you run a UNIX-like operating system such as
Linux or one of the BSDs, you could, once you
have everything installed the way you want it,
leave it running without rebooting it for months.
It is also likely that you won't install anything
for a long time as well. The
reason for this is that the CD ROM reader has sat
still for months, doing nothing. All that has
happened is that dust has been sucked through the
computer and where there is a shiny surface, it
has settled.
The
reason for this is that the CD ROM reader has sat
still for months, doing nothing. All that has
happened is that dust has been sucked through the
computer and where there is a shiny surface, it
has settled.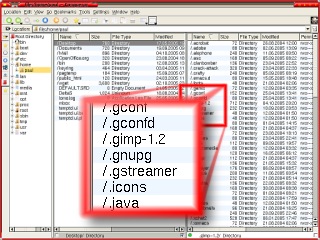 On Linux systems or
any UNIX-like OS including Mac OS X, OpenBSD, FreeBSD and
NetBSD, files and directories whose names start with a
dot are hidden by the system from normal operations such
as ls (directory listing).
On Linux systems or
any UNIX-like OS including Mac OS X, OpenBSD, FreeBSD and
NetBSD, files and directories whose names start with a
dot are hidden by the system from normal operations such
as ls (directory listing).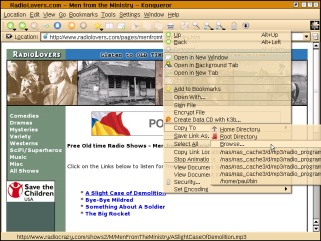
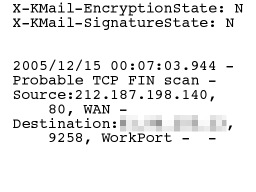 Sometimes,
people claim that they haven't been spending as much time
on a particular program as they really have - this is
usually browsers or instant messenger programs.
Sometimes,
people claim that they haven't been spending as much time
on a particular program as they really have - this is
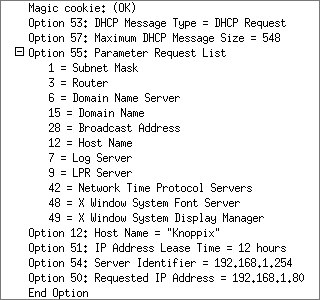
usually browsers or instant messenger programs.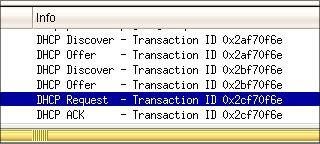 If
you have started off with a small network and
used the hosts files on each machine, you might
start to find that as you increase the number of
hosts on the network, the amount of work involved
with keeping each host's hosts files up-to-date
increases very quickly. The quick answer to this
is to use Dynamic Host Configuration Protocol
(DHCP). In the screenshot on the right, you can
see a typical exchange between a new host and the
server.
If
you have started off with a small network and
used the hosts files on each machine, you might
start to find that as you increase the number of
hosts on the network, the amount of work involved
with keeping each host's hosts files up-to-date
increases very quickly. The quick answer to this
is to use Dynamic Host Configuration Protocol
(DHCP). In the screenshot on the right, you can
see a typical exchange between a new host and the
server.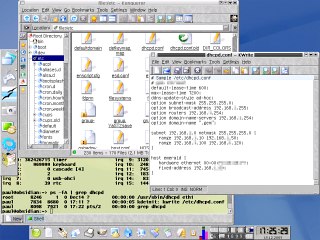
 Start
the server in a console by entering
Start
the server in a console by entering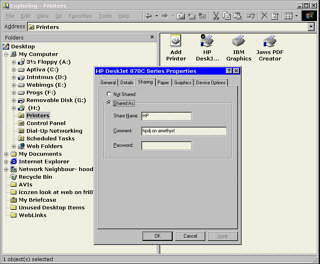 On the Windows machine (if it is
one), just enable network sharing and then, in
Windows Explorer, click on the Printer folder in
the tree in the left pane (under My Computer) and
then right click on the printer you want to
share.
On the Windows machine (if it is
one), just enable network sharing and then, in
Windows Explorer, click on the Printer folder in
the tree in the left pane (under My Computer) and
then right click on the printer you want to
share.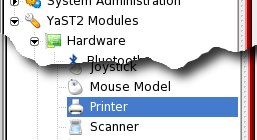 On your Linux box, open up the KDE
'Control Center' and in the tree on the left,
select 'YaST2 Modules'/ 'Printer'.
On your Linux box, open up the KDE
'Control Center' and in the tree on the left,
select 'YaST2 Modules'/ 'Printer'. Next, the configuration page
displays and it checks through its list. If this
is the first time, it will build up a database
which might take a minute.
Next, the configuration page
displays and it checks through its list. If this
is the first time, it will build up a database
which might take a minute.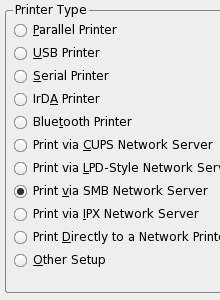 In the next page, click on the 'Add'
button then select the 'Print via SMB Network
Server' option and click on 'Next'.
In the next page, click on the 'Add'
button then select the 'Print via SMB Network
Server' option and click on 'Next'.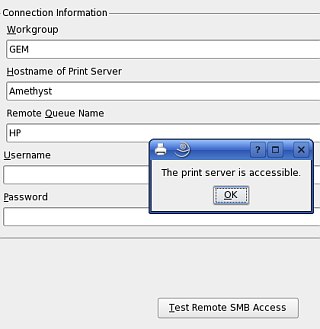 On the 'Connection Information'
form, you need to type the particulars of the SMB
server you need to use.
On the 'Connection Information'
form, you need to type the particulars of the SMB
server you need to use.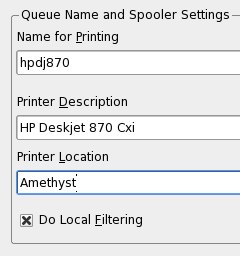 In 'Queue Name', give the name for
printing as something that is easy to type
because you might decide to do this using the
command line one day. Also, make the 'Printer
Description' fairly meaningful.
In 'Queue Name', give the name for
printing as something that is easy to type
because you might decide to do this using the
command line one day. Also, make the 'Printer
Description' fairly meaningful.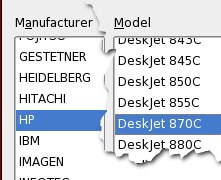 In 'Printer Model', select the
manufacturer and Model of the printer you are
using.
In 'Printer Model', select the
manufacturer and Model of the printer you are
using.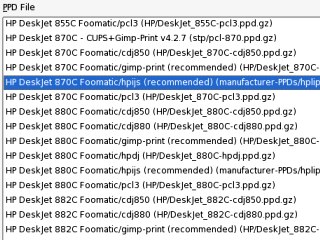 In the 'PPD Files' dialogue, you can
select specific drivers
In the 'PPD Files' dialogue, you can
select specific drivers If you do print the test page, it
should look like this.
If you do print the test page, it
should look like this.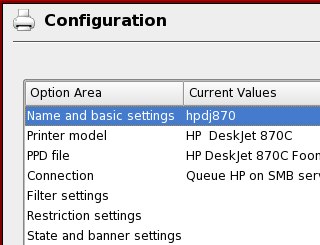 You should now see your printer in
the printer list. Click on 'OK'.
You should now see your printer in
the printer list. Click on 'OK'.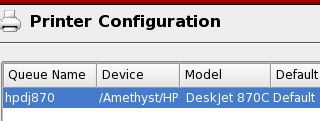 Now that to your configuration is
complete, click on 'OK'.
Now that to your configuration is
complete, click on 'OK'.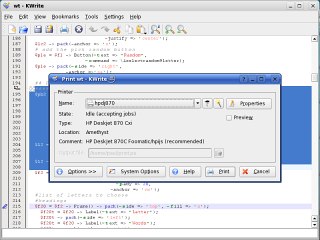 Next time you want to print
something, you should see the printer appear in
the printer list when you want to print a
document.
Next time you want to print
something, you should see the printer appear in
the printer list when you want to print a
document.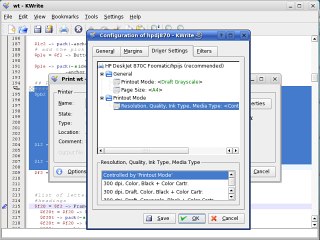 If you click on Properties, you can
change the printer configuration such as colour
depth and resolution.
If you click on Properties, you can
change the printer configuration such as colour
depth and resolution.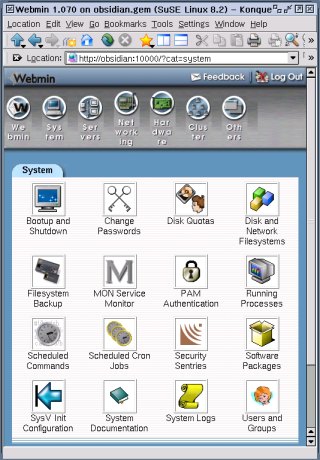 On
the local machine, you can use various
configuration files and programs to get the
system looking and working just the way you want
but if you want a central console from which you
have access to all of the machines on your LAN,
you need something that is designed to do the
job.
On
the local machine, you can use various
configuration files and programs to get the
system looking and working just the way you want
but if you want a central console from which you
have access to all of the machines on your LAN,
you need something that is designed to do the
job.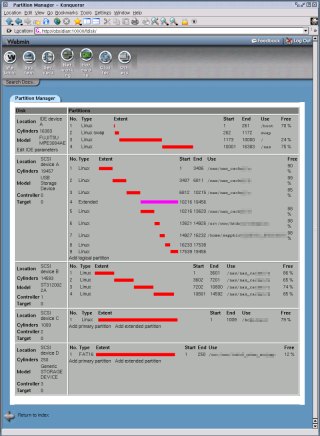 Instead
of using Webmin just for configuration, you can
use it to monitor some components of a system. In
the screenshot on the right, you can see disc and
partition usage - you can also use it to look at
your mail. There are many uses of this program
and you can see more about it at
Instead
of using Webmin just for configuration, you can
use it to monitor some components of a system. In
the screenshot on the right, you can see disc and
partition usage - you can also use it to look at
your mail. There are many uses of this program
and you can see more about it at 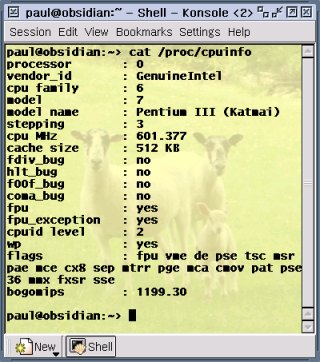 BOGOMIPS or bogus
MIPS is a measure of how fast the processor is and, like
any MIPS rating, it is open to abuse and misuse. It can
be used as an aid to get an appreciation about how fast a
given computer is but its primary reason for existing is
so allow Linux to function in a timely fashion where
timing is important.
BOGOMIPS or bogus
MIPS is a measure of how fast the processor is and, like
any MIPS rating, it is open to abuse and misuse. It can
be used as an aid to get an appreciation about how fast a
given computer is but its primary reason for existing is
so allow Linux to function in a timely fashion where
timing is important.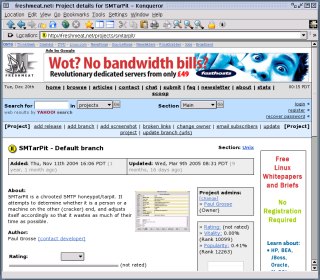 Open
Source software is usually seen as being run only
on UNIX-like systems such as the many flavours of
Linux or the BSD family (other Unices are also
catered for). However, there are plenty of
projects that also have ports to Windows and DOS.
Open
Source software is usually seen as being run only
on UNIX-like systems such as the many flavours of
Linux or the BSD family (other Unices are also
catered for). However, there are plenty of
projects that also have ports to Windows and DOS. These
are Sourceforge (
These
are Sourceforge (